Security and the Basics of Encryption in E-Commerce. … Encryption is a generic term that refers to the act of encoding data, in this context so that those data can be securely transmitted via the Internet.
What is encryption with example?
Encryption is defined as the conversion of something to code or symbols so that its contents cannot be understood if intercepted. When a confidential email needs to be sent and you use a program that obscures its content, this is an example of encryption.
What are common types of encryption in ecommerce?
There are two types of encryption in widespread use today: symmetric and asymmetric encryption.
What do you mean by encryption?
Encryption – definition and meaning Encryption in cyber security is the conversion of data from a readable format into an encoded format. Encrypted data can only be read or processed after it’s been decrypted. Encryption is the basic building block of data security.Why is encryption used?
In simple terms encryption is the process through which data is encoded so that it remains hidden from or inaccessible to unauthorized users. It helps protect private information, sensitive data, and can enhance the security of communication between client apps and servers.
What is encryption PDF?
Encrypting a PDF document protects its content from unauthorized access. Confidential PDF documents can be encrypted and protected with a password. Only people who know the password will be able to decrypt, open and view those documents.
What are encryption codes?
A Definition of Data Encryption Data encryption translates data into another form, or code, so that only people with access to a secret key (formally called a decryption key) or password can read it. Encrypted data is commonly referred to as ciphertext, while unencrypted data is called plaintext.
How do you do encryption?
- On your home computer, choose the file or folder you want to encrypt and right-click on it.
- Select Properties.
- Select the Advanced button then check the box next to Encrypt contents to secure data.
- Press OK, which will close the Advanced Attributes window.
What is encryption and data protection?
In general, encryption refers to the procedure that converts clear text into a hashed code using a key, where the outgoing information only becomes readable again by using the correct key. … Encryption is the best way to protect data during transfer and one way to secure stored personal data.
What are the 4 basic types of encryption systems?- Triple DES. Triple Data Encryption Algorithm or Triple-DES uses symmetric encryption. …
- RSA. …
- Blowfish. …
- Twofish. …
- Hashes. …
- Digital Certificates. …
- IPsec. …
- PPTP.
Which password types are encrypted?
The three major encryption types are DES, AES, and RSA.
What is the difference between hashing and encryption?
Hashing and encryption are the two most important and fundamental operations of a computer system. Both of these techniques change the raw data into a different format. Hashing on an input text provides a hash value, whereas encryption transforms the data into ciphertext.
How secure is encryption?
Generally, encryption is safe. Data transmitted and stored with encryption is safer than when left unencrypted. The average user uses encryption automatically many times a day when using a web browser or mobile app. Manual file encryption is safe with responsible handling of the decryption keys.
What is encryption and how does it work?
Encryption is the process of taking plain text, like a text message or email, and scrambling it into an unreadable format — called “cipher text.” This helps protect the confidentiality of digital data either stored on computer systems or transmitted through a network like the internet.
How do I find encryption code?
Check your device manual for supported encryption protocols. The default encryption key may be located on the bottom of your router or in the manual, depending on the router manufacturer. You can locate the encryption key when you log into the router setup page, if you have created your own encryption key.
What is encryption and decryption with example?
Encryption is the process of translating plain text data (plaintext) into something that appears to be random and meaningless (ciphertext). Decryption is the process of converting ciphertext back to plaintext. … To decrypt a particular piece of ciphertext, the key that was used to encrypt the data must be used.
How do I Encrypt Adobe?
Open a file in Acrobat and choose “Tools” > “Protect.” Select whether you want to restrict editing with a password or encrypt the file with a certificate or password. Set password or security method as desired. Click “OK” and then click “Save.”
What is encryption equipment?
Device encryption is the process of scrambling data into illegible code and making it indecipherable to anyone without a password or a recovery key. The data (referred to as ‘plaintext’) is encoded using an encryption algorithm to turn it into an unreadable format (referred to as ‘ciphertext’).
How do you Encrypt a PDF?
Add a password to Adobe Acrobat (pdf) Open the PDF and choose Tools > Protect > Encrypt > Encrypt with Password. If you receive a prompt, click Yes to change the security. Select Require a Password to Open the Document, then type the password in the corresponding field.
What is encryption of personal data?
Encryption is a mathematical function that encodes data in such a way that only authorised users can access it. It is a way of safeguarding against unauthorised or unlawful processing of personal data, and is one way in which you can demonstrate compliance with the security principle.
What is encryption of a file?
File encryption protects individual files or file systems by encrypting them with a specific key, making them accessible only to the keyholder. The goal is to prevent malicious or unauthorized parties from accessing files that are stored on the disk.
How do I encrypt a file online?
- Drag and drop your PDF to the toolbox above.
- Enter the password you’d like to set.
- Click ‘Encrypt PDF’ to add the password to the PDF.
- Download your encrypted PDF file!
What is decrypt tool?
Ransomware is a malware that locks your computer or encrypts your files and demands a ransom (money) in exchange. Quick Heal has developed a tool that can help decrypt files encrypted by the following types of ransomware. … The tool is free and can be used without any hassle.
What are two basic components of encryption?
In asymmetric, or public key, encryption, there are two keys: one key is used for encryption, and a different key is used for decryption. The decryption key is kept private (hence the “private key” name), while the encryption key is shared publicly, for anyone to use (hence the “public key” name).
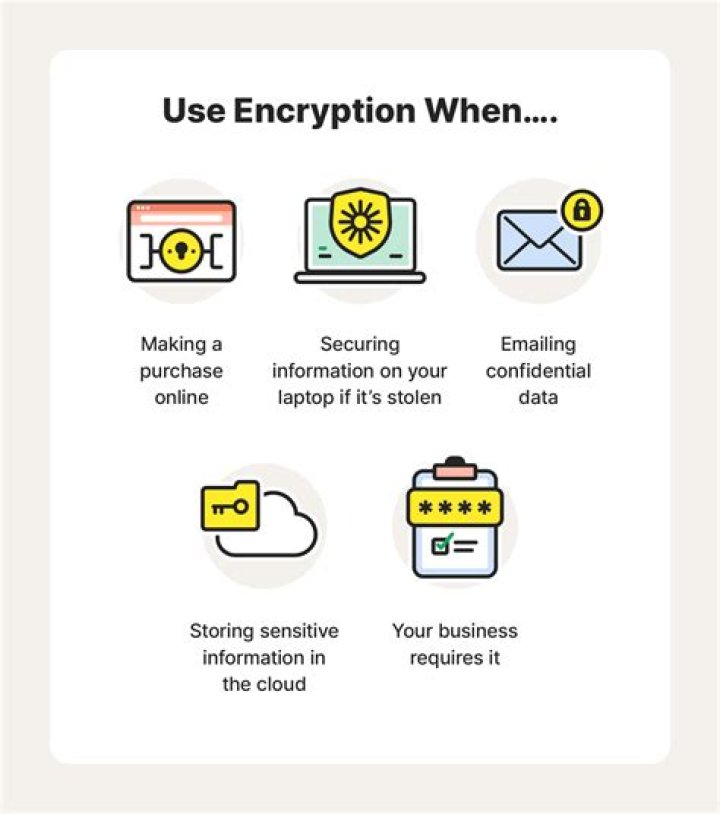
Where is encryption used today?
Encryption is used in electronic money schemes to protect conventional transaction data like account numbers and transaction amounts, digital signatures can replace handwritten signatures or a credit-card authorizations, and public-key encryption can provide confidentiality.
Which encryption is most secure?
The Advanced Encryption Standard, AES, is a symmetric encryption algorithm and one of the most secure. The United States Government use it to protect classified information, and many software and hardware products use it as well.
What is encryption Geeksforgeeks?
In an encryption scheme, the intended information or message, referred to a plaintext, is encrypted using an encryption algorithm, generating ciphertext that can only be read if decrypted.
What is difference between encode and encryption?
While encryption does involve encoding data, the two are not interchangeable terms, encryption is always used when referring to data that has been securely encoded. Encoding data is used only when talking about data that is not securely encoded. An example of encryption is: AES 256.
Why hash is used in encryption?
Hashing is a one-way encryption process such that a hash value cannot be reverse engineered to get to the original plain text. Hashing is used in encryption to secure the information shared between two parties. The passwords are transformed into hash values so that even if a security breach occurs, PINs stay protected.
What is AES 256-bit encryption?
What is 256-bit AES encryption? 256-bit AES encryption refers to the process of concealing plaintext data using the AES algorithm and an AES key length of 256 bits. In addition, 256 bits is the largest AES key length size, as well as its most mathematically complex. It is also the most difficult to crack.
What is AES and SHA?
SHA stands for Secure Hash Algorithm while AES stands for Advanced Encryption Standard. So SHA is a suite of hashing algorithms. AES on the other hand is a cipher which is used to encrypt.